Extended Detection and Response (XDR) unifies threat detection, investigation, and response across endpoints, networks, cloud, identity, and email into a single platform, replacing the siloed approach of running separate EDR, SIEM, and SOAR tools.
We researched 7 XDR solutions, verifying vendor claims against official product documentation, MITRE ATT&CK evaluation results, and customer deployments. See our analysis on value and performance comparison.
Table 1: Feature comparison of top 7 XDR solutions
XDR vs EDR vs SIEM
These three categories overlap significantly in vendor marketing, but each solves a different scope problem.
- EDR (Endpoint Detection and Response) monitors and responds to threats on endpoint devices, such as laptops, servers, and workstations. It collects telemetry from the endpoint agent, detects behavioral anomalies, and enables analysts to investigate and contain threats on individual devices.
- XDR extends EDR across multiple security layers. Where EDR covers the endpoint, XDR ingests and correlates telemetry from endpoints, networks, cloud workloads, identity systems, and email into a unified detection and response platform. Cross-domain correlation allows XDR to surface attack chains that appear as unrelated noise in separate tools.
- SIEM (Security Information and Event Management) collects and stores log data from across the environment for threat detection, compliance reporting, and historical investigation. Traditional SIEM is passive: it alerts on rule matches and stores data for queries. Modern SIEM platforms are converging with XDR and SOAR, with vendors like Microsoft (Sentinel + Defender XDR) and CrowdStrike (Falcon Next-Gen SIEM) treating SIEM as the data layer underneath an XDR detection engine.
Native XDR vs Open XDR
XDR market has formally bifurcated into two distinct architectural models that drive fundamentally different buying decisions.
- Native XDR is a single-vendor platform that integrates the vendor’s own endpoint, network, cloud, and identity products into a unified detection-and-response layer. CrowdStrike Falcon, Microsoft Defender XDR, and SentinelOne Singularity are native XDR platforms. The advantage is deep integration and a single data model; the trade-off is that you are purchasing into a vendor ecosystem.
- Open XDR is vendor-agnostic: it ingests telemetry from any existing security tool in the stack and provides unified detection, investigation, and response on top of those inputs without requiring rip-and-replace.
Comparison of Top 7 XDR Solutions
Ratings are based on G2, Gartner, and Capterra. Vendors are listed in order of their review counts.
Employee counts are based on LinkedIn data.
How do we choose the top XDR vendors?
When selecting XDR platforms for review, we applied the following publicly verifiable and objective criteria:
- Employee count: We focused on organizations with more than 50 employees as a proxy for organizational stability and capacity for product investment.
- User reviews: We required a minimum of 30 reviews on B2B review platforms (G2, Gartner Peer Insights, Capterra), indicating some market presence validated by real deployments.
- Core feature coverage: Solutions must provide cross-domain telemetry ingestion, unified incident detection and response, and documented MITRE ATT&CK alignment to qualify as XDR rather than standalone EDR.
Table 2: Feature comparison of the top 7 XDR solutions
1. Stellar Cyber Open XDR
Stellar Cyber is the leading Open XDR platform, built on a vendor-agnostic architecture that ingests telemetry from any existing security tool through 400+ prebuilt connectors.1 Rather than requiring organizations to replace their current EDR, NGFW, or identity tools, Stellar Cyber sits on top of the existing stack and provides unified detection, investigation, and response across all inputs.
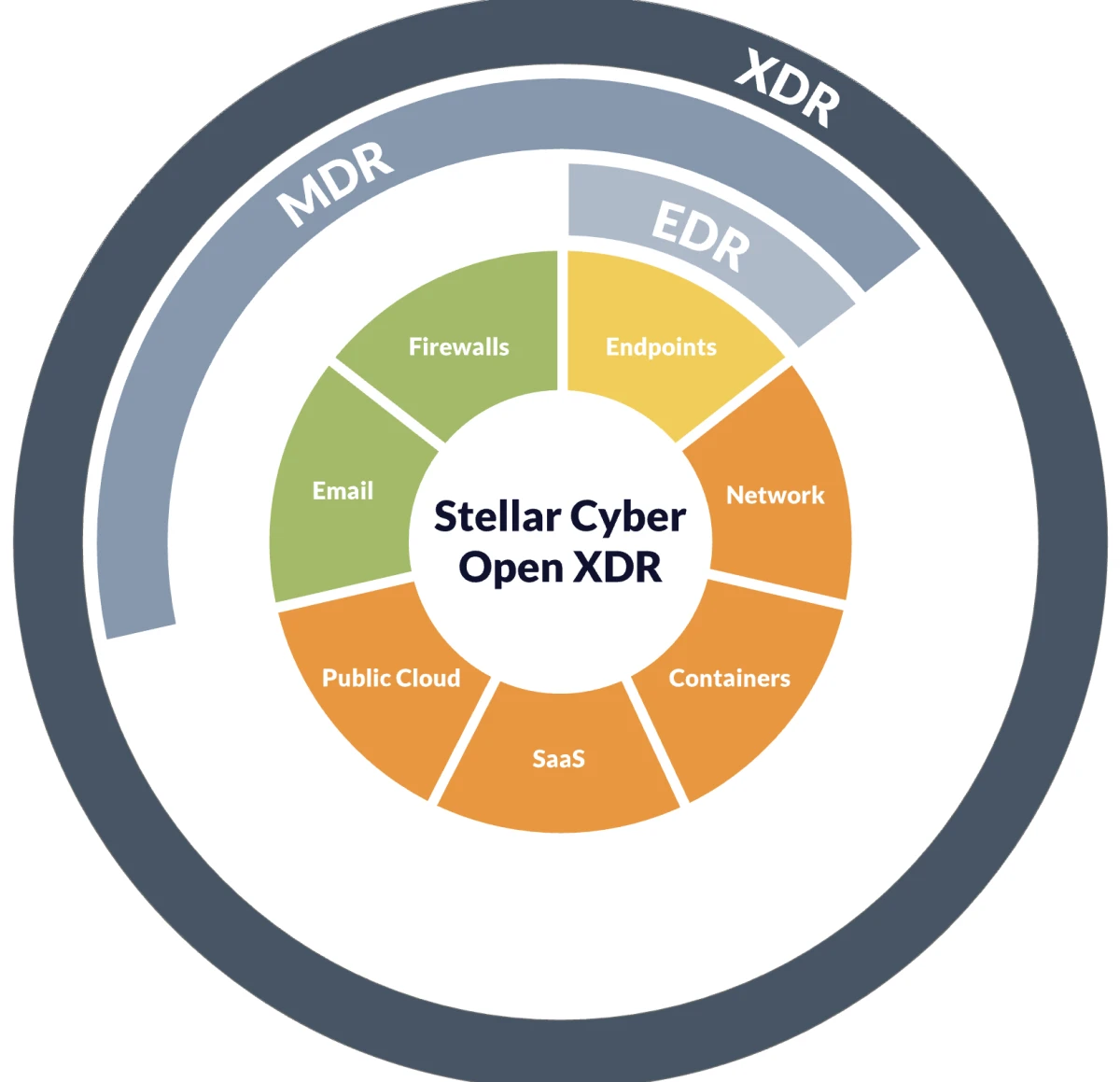
Source: Stellar Cyber
Key features:
- Open architecture: 400+ connectors ingesting from any EDR, NGFW, identity provider, or cloud platform
- Single license covering SIEM, NDR, XDR, and UEBA
- Interflow event modeling for cross-source attack chain correlation
- AI-driven triage, alert correlation, and case building
- Agentic AI capabilities for initial investigation and case summarization
Limitations:
- The platform is optimized for organizations with 50–500 employees and mid-market security teams; enterprise-scale customization and advanced forensic depth may lag behind CrowdStrike and Palo Alto
- Open XDR’s breadth of ingestion requires careful connector configuration; detection quality depends on telemetry quality from source tools
- Smaller partner and integration ecosystem than native XDR vendors with longer market presence
2. SentinelOne Singularity XDR
SentinelOne Singularity XDR is a native XDR platform known for its AI-driven detection and response at the endpoint layer, extended to cloud workloads, identity, and network through a single unified data lake.
Purple AI is SentinelOne’s natural-language threat hunting interface, allowing analysts to query the Singularity Data Lake in plain English and receive investigation summaries, threat hunt results, and recommended remediation steps.
Key features:
- Autonomous threat detection and one-click rollback for ransomware without analyst intervention
- Storyline for automatic root cause analysis and attack narrative construction
Limitations:
- Some users report that overly aggressive blocking of legitimate tools, including developer applications, has been blocked, requiring manual exception management
- Agent duplication issues have been reported in the management console during large-scale deployments
3. CrowdStrike Falcon XDR
CrowdStrike Falcon XDR is a native XDR platform built on a single lightweight agent and a cloud-native data architecture. The platform spans 30 modules covering endpoints, cloud workloads, identity, and SIEM, with XDR correlation running across all domains via a shared data lake.
- CrowdStrike achieved 100% detection with zero false positives in its most recent MITRE ATT&CK evaluation, the company’s strongest cross-domain result to date2
- CrowdStrike announced an expanded partnership with Intel to optimize the Falcon platform for Intel-powered AI PCs, combining Falcon’s endpoint intelligence with Intel’s silicon-level telemetry and NPUs to protect AI workloads executing directly on the device.3 Also at RSAC 2026, CrowdStrike announced new cloud security and data protection capabilities addressing how to prioritize cloud risks based on real attacker behavior and how to protect sensitive data moving across endpoints, SaaS, cloud, and generative AI tools.
- As of Q3 FY2026, 49% of CrowdStrike subscription customers had adopted six or more Falcon modules, and the platform crossed $5 billion in annual recurring revenue.4
Key features:
- Single lightweight agent across endpoint, cloud workload, identity, and SIEM
- Charlotte AI for natural-language threat investigation and triage
- Agentic MDR with human oversight for organizations without in-house SOC capacity
Limitations:
- Platform breadth and a 30-module architecture creates significant procurement complexity; buyers need to map specific modules to specific use cases before quoting
- Falcon sensor deployment is required for full XDR data fidelity on endpoints; organizations restricted from agent deployment will have gaps
4. Cisco XDR
Cisco XDR is a cloud-native XDR platform that replaced the retired Cisco SecureX. Cisco XDR correlates telemetry from Cisco’s security portfolio and third-party integrations. Organizations evaluating Cisco’s detection and response capabilities should reference Cisco XDR, not SecureX, which has been fully retired.
The platform is a natural fit for organizations already using Cisco’s networking and security infrastructure, where native telemetry correlation among Cisco Secure Firewall, Catalyst switches, and endpoint agents significantly reduces integration overhead.
Key features:
- Native integration across Cisco’s security portfolio (endpoint, network, email, identity)
- Third-party integrations extending coverage beyond the Cisco ecosystem
- Automated incident investigation with prioritized alert correlation
- Integration with Cisco Talos threat intelligence
Limitations:
- Value is significantly higher for organizations invested in Cisco’s existing security portfolio; organizations running non-Cisco infrastructure will see less native integration benefit
- Cisco XDR is a relatively recent product; feature depth in some areas lags more established native XDR platforms
- Unlike SecureX, which was included free with Cisco security licenses, Cisco XDR requires a separate paid license a meaningful cost change for existing Cisco customers
5. Exabeam New-Scale Security Operations Platform
Exabeam was previously positioned as a SIEM and XDR platform. As of January 2026, Exabeam markets its primary offering as the New-Scale Security Operations Platform (sold as New-Scale Fusion), reflecting expanded capabilities that go beyond traditional SIEM and XDR functions.5
Key features:
- New-Scale Fusion platform: SIEM, UEBA, and XDR in a unified architecture
- Agent Behavior Analytics (ABA) for AI agent monitoring (January 2026)
- AI Usage Security for detecting risky employee AI tool interactions
- Behavioral analytics with 50+ pre-built threat scenarios mapped to MITRE ATT&CK
- Integration with 500+ security and IT data sources
- Outcome-based use cases with pre-packaged content for common threat types
Limitations:
- Platform rebrand from SIEM+XDR to New-Scale creates procurement confusion; buyers should verify which capabilities are included in base licensing vs. add-ons
- ABA and AI Usage Security are newly launched; production maturity and detection coverage should be validated before relying on them for critical use cases
6. Microsoft Defender XDR
Microsoft Defender XDR is a native XDR platform that correlates signals across Microsoft Defender for Endpoint, Defender for Identity, Defender for Office 365, and Microsoft Sentinel into a unified incident investigation experience.
The platform’s primary competitive advantage is ecosystem integration: native connectivity to Entra ID, Intune, Azure, and the full Microsoft 365 stack eliminates the integration work required to achieve the same coverage with a third-party XDR. Microsoft Sentinel serves as the underlying SIEM and data lake.
Key features:
- Unified incident view correlating signals across endpoint, identity, email, and cloud
- Microsoft Sentinel as the SIEM and SOAR layer with 500+ data connectors
- Security Copilot integration for natural-language investigation and report drafting
Limitations:
- Detection efficacy is strong on Windows, but weaker on macOS and Linux endpoints. Non-Microsoft-stack environments may require layered coverage
- Governance of the platform requires navigating multiple consoles (Defender portal, Sentinel workspace, Entra admin center), which increases analyst cognitive load compared to single-console competitors
- Licensing tiers (E3, E5, Defender add-ons, Copilot for Security) are complex; total cost requires careful mapping
7. Palo Alto Cortex XDR
Palo Alto Networks Cortex XDR is a native XDR platform that integrates endpoint, network, and cloud telemetry with Palo Alto’s firewall and Prisma infrastructure to provide a unified detection and response layer.
Cortex XSIAM is Palo Alto’s full-platform response to the agentic SOC market. While Cortex XDR handles detection and response for endpoint and network, Cortex XSIAM consolidates SIEM, XDR, SOAR, and attack surface management into a single platform powered by 10,000+ detectors and 2,600+ ML models, with 500+ pre-built automation playbooks.6
Key features:
- 100% technique-level detection in MITRE ATT&CK Round 6
- Behavioral threat protection across endpoint, network, cloud, and identity from a single agent
- Incident views that stitch alerts into a single attack storyline with root cause and blast radius
- Native integration with Palo Alto firewalls and Prisma SASE for combined network and endpoint visibility
Limitations:
- Best value is achieved within the Palo Alto ecosystem (firewalls, Prisma); organizations without existing Palo Alto infrastructure face higher deployment overhead
- Cortex XDR is consistently rated at the premium end of the XDR pricing spectrum; the model’s total cost of ownership is early, including PRO licensing
Common Features
All platforms reviewed include the following as standard capabilities:
- Cross-domain telemetry ingestion: All platforms ingest data from an endpoint and at least one additional security domain (network, cloud, identity, or email). Coverage breadth and depth vary; buyers should map their specific telemetry sources against each vendor’s connector catalog before shortlisting.
- Unified incident detection: All platforms correlate multi-source telemetry into consolidated incidents, rather than surfacing individual alerts from each tool. This is the core XDR value proposition that differentiates it from standalone EDR.
- MITRE ATT&CK alignment: All platforms map detections to MITRE ATT&CK tactics and techniques, enabling consistent threat categorization and gap analysis against the framework.
- Automated response actions: All platforms support automated or semi-automated response isolating endpoints, blocking IPs, and revoking credentials, though the degree of automation and the domains covered vary significantly.
- Threat intelligence integration: All platforms include or integrate threat intelligence feeds. CrowdStrike (Adversary Intelligence), Palo Alto (Unit 42), and Cisco (Talos) operate proprietary threat research teams with global coverage.
- Compliance logging and reporting: All platforms maintain audit-ready logs of detection and response activity. SIEM-integrated platforms provide broader compliance coverage.
AI-Driven XDR
- AI-assisted detection uses machine learning models trained on adversary behavior to identify threats that evade signature-based rules. Anomaly detection, peer-group behavioral analysis, and indicators of attack (IOAs) are the primary mechanisms. CrowdStrike’s IOA framework, SentinelOne’s Storyline, and Palo Alto’s 2,600+ ML models in XSIAM represent mature implementations of this approach.
- Natural-language investigation allows analysts to query platform data and generate investigation summaries in plain language. SentinelOne Purple AI, Microsoft Security Copilot, CrowdStrike Charlotte AI, and Exabeam’s natural-language querying all allow analysts to ask questions like “what lateral movement occurred in the last 72 hours,” rather than writing detection queries manually.
- Agentic AI: AI systems that autonomously execute multi-step investigation and response workflows without human intervention at each step are the most-marketed capability in XDR in 2026, and the most overstated. According to a March 2026 report based on 30+ vendor briefings and CISO interviews, most production deployments of agentic SOC capabilities are handling enrichment, summarization, and report drafting, not autonomous remediation. Gartner places AI SOC agents at 1–5% enterprise adoption. CrowdStrike Agentic MDR, Microsoft Security Alert Triage Agent, and Exabeam ABA represent the most clearly scoped agentic capabilities announced to date; all retain human oversight for high-stakes decisions.7
Top 8 XDR Use Cases
- Ransomware detection and response: XDR correlates endpoint behavioral indicators (process injection, shadow copy deletion, mass file encryption) with network anomalies and identity activity to detect ransomware before encryption completes, and to identify the full lateral movement path that preceded it.
- Insider threat detection: Cross-domain correlation of unusual access patterns, after-hours data downloads, and deviations from behavioral baselines surfaces insider threats that EDR alone cannot detect. Exabeam and Stellar Cyber are strongest in this use case due to UEBA foundations.
- Credential-based attack detection: Most enterprise breaches in 2026 do not involve malware; attackers use valid credentials to move laterally. XDR correlates identity telemetry (impossible travel, MFA bypass, new device registration) with endpoint and network data to surface credential abuse that password monitoring alone misses.
- Cloud workload threat detection: As workloads move to AWS, Azure, and GCP, XDR platforms extend endpoint-style detection to cloud VMs, containers, and serverless functions. CrowdStrike and SentinelOne have the deepest cloud workload coverage; Microsoft Defender XDR is strongest within Azure.
- Supply chain and third-party compromise detection: XDR correlates initial access from a third-party connector or software update with subsequent lateral movement to identify supply chain intrusion at the point of initial execution rather than weeks into an attack.
- SOC alert consolidation: Organizations running separate EDR, SIEM, and network monitoring tools typically manage alert queues from each separately. XDR consolidates these into unified incidents, reducing alert volume and the context-switching that causes analyst fatigue.
FAQs
Extended Detection and Response (XDR) is a security platform category that ingests and correlates telemetry from multiple security layers into a unified detection, investigation, and response system. XDR replaces the siloed approach to managing separate EDR, SIEM, and SOAR tools by surfacing attack chains that span multiple domains rather than alerting on each event in isolation.
EDR (Endpoint Detection and Response) monitors and responds to threats on individual endpoint devices. XDR extends that scope: it ingests EDR telemetry alongside data from networks, cloud, identity, and email, then correlates all of it into cross-domain incident views. The practical difference is that EDR shows what happened on a machine; XDR shows what the attacker did across the entire environment before and after compromising that machine.
Native XDR is a single-vendor platform that integrates the vendor’s own security products. CrowdStrike, Microsoft, SentinelOne, and Palo Alto are examples. Open XDR ingests data from any existing security tool, regardless of vendor, and sits on top of the current stack without requiring a replacement. Organizations consolidating onto a single vendor should evaluate native XDR; organizations with heterogeneous tool stacks they want to retain should evaluate Open XDR platforms like Stellar Cyber.
Telemetry ingestion: The XDR platform collects data from deployed agents (endpoint), network sensors, cloud APIs, identity providers, and email security tools. Native XDR platforms ingest data from their own product suite; Open XDR platforms ingest data from any source via prebuilt connectors.
Normalization and correlation: Raw telemetry is normalized into a common data schema. The platform’s detection engine correlates events across sources, for example, linking a suspicious login from identity logs to an unusual process execution from the endpoint agent and a cloud API call from the workload layer, and surfaces these as a single incident rather than three separate alerts.
AI-assisted detection: Machine learning models trained on patterns of adversary behavior (often mapped to MITRE ATT&CK) detect anomalies that rule-based systems miss. Most platforms now include some form of AI-assisted triage, though the depth varies significantly between vendors.
Investigation and response: Analysts work from a unified incident view showing the full attack chain across domains. Response actions can be executed directly from the platform. Some platforms automate response steps via built-in SOAR capabilities.

Be the first to comment
Your email address will not be published. All fields are required.